The Rise of Vibe Coding: Careless Hype or Future Prototyping?
Vibe coding is building software by describing what you want in natural language and iterating on the output “vibe”—often without deeply reading the code. It’s real, it’s useful, and it’s not going away: Collins named “vibe coding” Word of the Year 2025, noting the shift toward AI-generated code from plain-English intent. (collinsdictionary.com)
But the tension is also real: vibe coding can collapse at scale if teams treat generated code as a black box. The fix isn’t “no vibes allowed.” The fix is a workflow upgrade: vibe for speed, then verify for trust—tests, threat modeling, dependency controls, and human review.
This article explains the rise, the risks, and the practical playbook.
What is “vibe coding,” really?
The cleanest definition comes from the person who popularized it: AI researcher Andrej Karpathy described “vibe coding” as a mode where you “fully give in to the vibes” and can “forget that the code even exists.” (x.com)
In practice, vibe coding usually looks like this:
- You describe an app or feature in plain language.
- The AI generates code (often across multiple files).
- You run it, look at the UI/behavior, and say things like:
- You repeat until it feels right.
The key move is that the developer optimizes for visible outcomes (the “vibe”) more than verified correctness (tests, security properties, maintainability). That’s why vibe coding can feel like creative flow… and why it can also create fragile systems.
Collins’ Word of the Year write-up explicitly frames vibe coding as turning natural language into code via AI, and highlights its cultural traction. (collinsdictionary.com)
Why vibe coding exploded in 2025–2026
Vibe coding didn’t blow up just because models improved. It blew up because the product layer around models changed: tools started acting like agents, not autocomplete.
Agentic IDEs and “WYSIWYG 2.0”
Modern vibe coding tools increasingly combine:
- natural-language instructions,
- multi-file edits,
- environment setup,
- and one-click deployment.
You can see this pattern across popular platforms:
- Cursor positions itself as an AI editor with “agents” and highlights Composer for larger, multi-step changes. (cursor.com)
- Replit Agent explicitly says it can set up and create apps from scratch “in minutes” from everyday language. (docs.replit.com)
- Lovable markets itself as a full-stack AI dev platform to build, iterate, and deploy web apps using natural language—with “real code” and governance features. (docs.lovable.dev)
- Vercel v0 frames vibe coding as rapid prototyping, while emphasizing that speed increases risk if you skip safety fundamentals. (vercel.com)
The economic reason: prototypes got cheap
When software goes from “weeks + a team” to “hours + prompts,” you get a new behavior: disposable prototypes and lightweight internal tools that exist to answer one question:
“Should we build this for real?”
That’s not inherently bad. In fact, it’s often exactly right for MVPs, experiments, and temporary workflows. Business media has noted the rise of “disposable apps” as AI makes app-building faster and cheaper. (businessinsider.com)
The great schism: velocity vs. verifiability
Vibe coding created a cultural split in tech:
- Accelerationists argue the cost of building software is collapsing, and people should build bespoke tools instead of paying for bloated SaaS subscriptions.
- Technocrats and enterprise builders warn that unverified code creates a quality and security crisis—especially once products scale.
A widely shared flashpoint was the public back-and-forth involving Y Combinator’s Garry Tan and Zoho’s Sridhar Vembu in early December 2025, arguing about whether vibe coding could “compete away” traditional SaaS. Multiple outlets covered the exchange and its underlying disagreement about reliability, guarantees, and long-term maintenance. (livemint.com)
Vembu’s critique is blunt: without strong guarantees (security, compliance, maintainability), vibe coding “piles up tech debt” until systems break under real-world demands. (x.com)
The truth is: both sides are pointing at something real.
- For 0→1 (prototype to proof), vibe coding is a superpower.
- For 1→N (scaling to reliability), vibe coding becomes a liability unless verification becomes the core workflow.
That brings us to the most important concept in this whole debate.
The verification bottleneck: the hidden tax on AI speed
AI can produce code faster than humans can audit it.
That mismatch creates a “trust gap”: the code looks like progress, but nobody has verified edge cases, threat models, performance, or maintainability. SonarSource describes this as a shift where generation is accelerating while verification becomes the bottleneck. (sonarsource.com)
In traditional development, humans write code at human speed—review naturally keeps pace.
In vibe coding, output can jump by thousands of lines in minutes—review often can’t keep up, so it gets skipped.
Result: apparent quality rises quickly (demo-ready UI), while actual quality may quietly decay.
The anatomy of AI technical debt
Technical debt is not new. What’s new is how vibe coding produces it.
1) Churn and regeneration instead of refactoring
When builders don’t fully understand the code, they often “prompt again” instead of refactoring. That encourages short-term churn and duplicated solutions.
GitClear’s research on AI-assisted code quality flags rising duplication and churn patterns associated with heavy AI usage. (gitclear.com)
2) Boilerplate bloat and “helpful” complexity
LLMs frequently generate verbose scaffolding—extra abstraction, redundant checks, inconsistent patterns. It feels safe in the moment, but it raises future cognitive load.
3) Architectural drift
Even with large context windows, agents still make local decisions that can conflict globally. The result can be a codebase that looks modular but behaves like spaghetti.
Industry coverage of AI-generated code has repeatedly highlighted architectural and security anti-patterns that appear systematically in generated output. (infoq.com)
Security risks: where vibe coding gets dangerous fast
If vibe coding is “prompt → code → ship,” attackers will happily meet you at “ship.”
Slopsquatting: weaponizing hallucinated dependencies
One of the most cited supply-chain risks is slopsquatting: models hallucinate plausible package names, and attackers publish malicious packages with those names—waiting for someone to npm install them.
- Trend Micro documents slopsquatting as an AI-driven supply chain risk tied to hallucinated packages. (trendmicro.com)
- Multiple security vendors have published explainers and mitigations (e.g., Mend, Snyk, FOSSA). (mend.io)
Insecure-by-default patterns
AI code generation can also increase the probability of insecure defaults (weak auth flows, missing input validation, improper secret handling). A Georgetown CSET report outlines broad risk categories around AI-generated code, including insecure outputs and downstream cybersecurity impacts. (cset.georgetown.edu)
Bottom line: Vibe coding is safest when you treat security like a first-class feature, not a final step.
So… is vibe coding careless hype?
It’s not hype. Collins doesn’t name something Word of the Year because it’s imaginary—and the tool ecosystem is now robust enough that “prompt-to-prototype” is normal. (collinsdictionary.com)
But careless vibe coding (ship-without-verification) is a real foot-gun—especially beyond prototypes.
A helpful framing:
Vibe coding is the future of prototyping.
Verified engineering is the future of production.
Even Andrej Karpathy has recently discussed the evolution from vibe coding toward more autonomous “agentic” workflows—suggesting the space is moving quickly, and expectations will keep shifting. (businessinsider.com)
The “Vibe, then Verify” playbook (practical and repeatable)
Here’s a workflow that preserves the upside of vibe coding while limiting the downside.
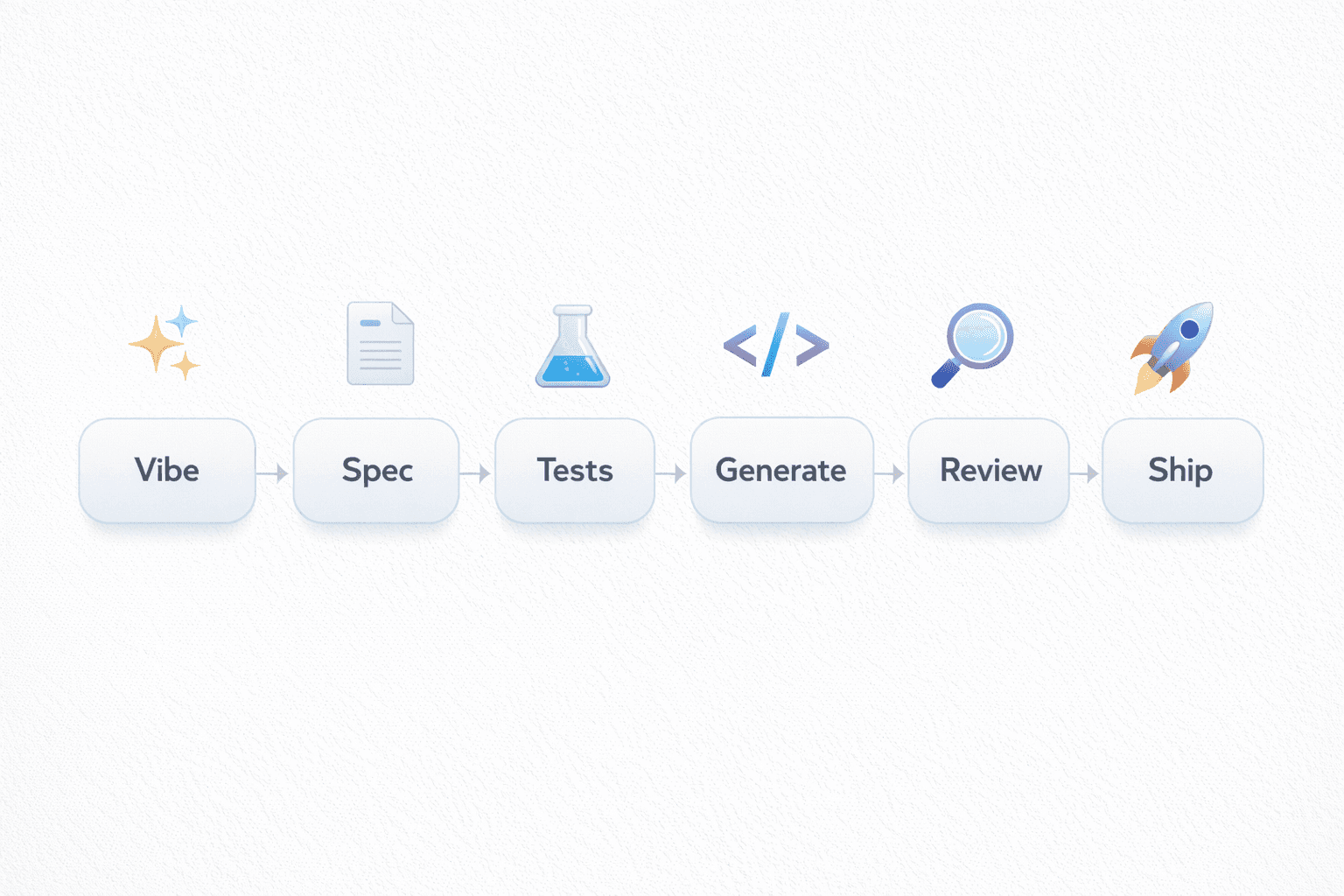
Step 1: Prompt the plan before you prompt the code
Instead of:
- “Build me a billing system”
Try:
- “Draft a technical plan for a billing system with roles, edge cases, and threat model. Then propose a minimal MVP.”
This forces structure early, when changes are cheap.
Step 2: Make the AI generate tests first
Ask for:
- unit tests (core logic),
- integration tests (API + DB),
- and security-focused tests where relevant.
Example prompt:
Write a test plan + tests for this feature before coding it:
- Success paths
- Failure paths
- Permission checks
- Input validation
- Rate limiting assumptions
Use Jest + Playwright. Assume Node + Postgres.Step 3: Lock down dependencies (anti-slopsquatting)
Adopt at least two controls:
- Allowlist dependencies for production (approved packages only).
- Require package lockfiles and review changes to them.
- Run dependency scanning (SCA) and SBOM generation in CI.
Step 4: Use static analysis + secret scanning in CI
A minimal “trust pipeline” might include:
- lint + type checks,
- SAST,
- secret scanning,
- dependency scanning,
- tests on every PR.
Example CI skeleton (illustrative):
name: ci
on: [push, pull_request]
jobs:
verify:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- uses: actions/setup-node@v4
with:
node-version: 20
- run: npm ci
- run: npm run lint
- run: npm test
- run: npm run buildStep 5: Require human review for “risk code”
Define what must be reviewed by an experienced engineer:
- auth & permissions
- payments
- encryption / secrets
- data deletion & retention
- anything that touches customer PII
- infra / deployment scripts
Step 6: Treat generated code as a draft, not an artifact
Use AI output as:
- a reference implementation,
- scaffolding,
- or a starting point—
…but keep engineering ownership: refactor, simplify, document decisions, and delete what you can’t justify.
Which vibe coding tools should you consider?
Tool choice depends on your goal. A simple heuristic:
- UI-first prototypes: v0, Lovable (fast iteration, visual outcomes) (vercel.com)
- Full-stack + deployment speed: Replit Agent (idea → running app quickly) (docs.replit.com)
- Developer workflow augmentation: Cursor (agentic IDE patterns, multi-step editing) (infoq.com)
Note: “best tool” lists shift quickly; treat them as discovery aids, not gospel. (techradar.com)
The future: verification becomes the real senior skill
If code is abundant, trust is scarce.
That’s why the most valuable engineers in an AI-heavy world won’t just be fast code writers—they’ll be:
- sharp reviewers,
- systems thinkers,
- and verification experts.
The job shifts from “type code” to “design + verify + operate.” And the teams that win will be the ones who can vibe quickly without shipping mysteries.
FAQ
Is vibe coding the same as no-code or low-code?
Not exactly. No-code/low-code typically uses constrained visual builders. Vibe coding uses natural language + generative code, often producing full codebases you can export and run. (vercel.com)
Is vibe coding safe for production apps?
It can be—if you apply verification: tests, reviews, security scanning, dependency controls, and operational discipline. Without those, supply-chain and insecure-code risks increase. (cset.georgetown.edu)
Can non-technical founders vibe code an MVP?
Yes, and it’s one of vibe coding’s strongest use cases—MVPs, demos, internal tools. Just plan for an engineering handoff (or a verification workflow) before real scaling. (docs.replit.com)
Does vibe coding replace developers?
It changes what “developer” means. Routine scaffolding is easier, but verification, architecture, security, and operations become more important—not less. (sonarsource.com)
What’s one mistake to avoid immediately?
Blindly installing dependencies suggested by an LLM. Slopsquatting exists specifically to exploit that behavior. (trendmicro.com)